"Activist infrastructures are where the messy, grinding, generally invisible labor of 'doing feminism' takes place." – Cait McKinney, Information Activism: A Queer History of Lesbian Media (2020).[1]
Being part of internets
Systerserver, a feminist server project of almost two decades,[2] has supported the ServPub project with their network infrastructure. The feminists involved in this project have configured their own infrastructure of two physical servers in the data room of [mur.at], an art association in Graz, Austria, which hosts a wide variety of art and cultural initiatives. The physical servers found this shelter through the networking of activists and artists during the Eclectic Tech Carnival (/ETC), a self-organised skill-sharing gathering. Donna Meltzer and Gaba from Systerserver went to Graz to upgrade the servers' hardware in 2019. The first machine, installed and configured in 2005, is called Jean and was refurbished by ooooo in 2023 during their stay in Graz for the Traversal Network of Feminist Servers (ATNOFS), which took place in different countries.[3] The ATNOFS event in Austria was hosted by ESC, a local media art gallery in Graz, which is affiliated with [mur.at].
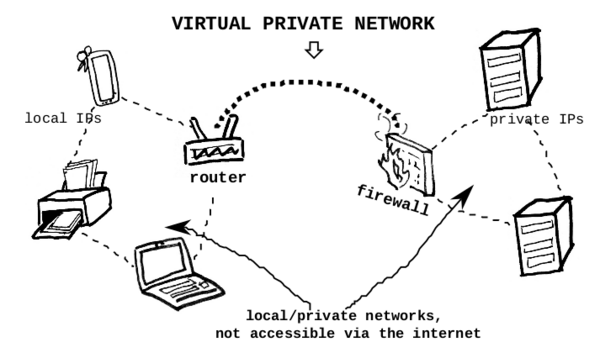
Both servers are running on Debian, a Linux-based operating system, and host several tools for community communications and organising,[4] among which is Tinc – a virtual private network (VPN) software. The VPN is the most recent addition, facilitating the desire for servers hosted by our peers from their homes, studios, and spaces that cannot afford a stable digital address.[5] Those server projects interweave into a feminist networking – an affective, socio-technical infrastructure – enabling more trans-feminist groups and collectives – such as actinomy (Bremen), leverburns (Amsterdam), caladona (Barcelona), or brknhs (Berlin) – to host their own servers in their own spaces rather than in data centres, and be reachable through the public internet.
Tinc was chosen as VPN software, mimicking what Systerserver learnt during their participation in ATNOFS, encountering the mobile server Rosa.[6] Rosa is a server connected to the internet via a VPN, hosted by the Rotterdam-based space Varia, which was inspired by another relevant network infrastructure setup – that of the Rotterdam-based institute XPUB.[7] Constant association in Brussels and Hackers and Designers collective in Amsterdam have also experimented with similar VPN-based servers.[8] The people, groups, and spaces involved in these server experiments often overlap, which is also due to the physical proximity of the projects (Rotterdam, Brussels, Amsterdam).
Being a server
A VPN software creates virtual private networks, connecting computers and devices that are not in the same physical location. In contrast to the public internet, the network between these devices is concealed – hence the term "private" – as it exists only between the trusted devices that have been added to it. A VPN can also provide a public entry point to these privately networked devices, making them reachable over the public internet and thus allowing them to function as servers. When devices connect to the internet, they are assigned a numeric identifier known as an Internet Protocol (IP) address. A home or office router is assigned a public IP address by its Internet Service Provider (ISP) – this address changes periodically, thus is referred to as dynamic. The ISP allocates these public IP address from a limited pool; each has an expiration period knowns as lease time. Once the lease expires, the address may change, allowing the ISP to provide internet connection to far more locations than the size of its IP pool. ISPs do this to manage available addresses more efficiently and for minor security benefits.[9]
All devices within a home or office are assigned a local IP address by the router. By default, the router permits one-way internet traffic – such as websites' content (response) – while blocking unsolicited traffic from the outside world. However, within a VPN network, the devices are assigned a private IP by the VPN software itself, and they become able to both send and receive traffic from outside their physical location.
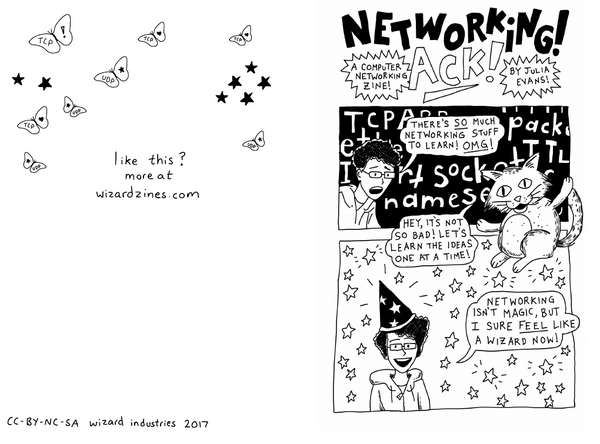
Visiting a device over the internet by remembering its IP address would be challenging, if not impossible. This is why domain names – such as www.servpub.net– are needed. They are mapped to an IP address so that when the domain name is visited, the browser can retrieve and present the content (for example, a website) hosted on that device. Maintaining the same IP address over time is crucial for reliably mapping it to a domain name. Such an address is therefore known as a fixed or static IP. The translation between IP addresses and domain names (and vice versa) is handled by Domain Name Servers, or DNS.[10]
So if a request is made to wiki4print.servpub.net, the request first reaches Jean, whose IP is mapped to that domain, because Jean is the only computer with a public and static IP address within this private network. On Jean, web engine configuration software forwards the request to the private IP of the device that actually hosts ServPub project's wiki. The request is thus rerouted internally – inside the concealed virtual private network – to the specific device hosting the wiki4print website. This forwarding of requests from the public IP to the private one is called a proxy request, and the device's ability to send data back through the public node – thus functioning as a server – is enabled via a reverse proxy.
Systerserver has configured three such private networks using Tinc to reach home-based servers that lack public and static IP address: internes, alliances and systerserver.[11] The network named systerserver was the first Tinc installation and configuration in Systerserver's infrastructure. It was initiated specifically for the publishing infrastructure of the ServPub project. The systerserver network allows the Raspberry Pis – which host wiki4print and the ServPub website – to be accessible over the internet via Systerserver's public node and machine, Jean.
Arriving at this first technical attempt to configure the systerserver network required building trust between Systerserver peers and the other groups participating in the ServPub project. This began with Winnie Soon's participation in one of Systerserver's week-long event and workshops in Barcelona in 2023, during which Systerserver installed PeerTube for and with the caladona women's space. Such collective, grassroots organising-based events – messy and campy – form the basis for bonding and solidarity, built on the invisible labour of doing feminism (McKinney 2020). By understanding computing together, configuring machines, and conversing about big tech and its sexism, racism, classism, and gender discrimination, the people gathered at these events nourish a resistance rooted in body and identity politics – one that transgress labour exchanges based on economic value alone.
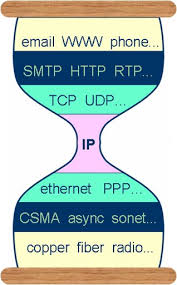
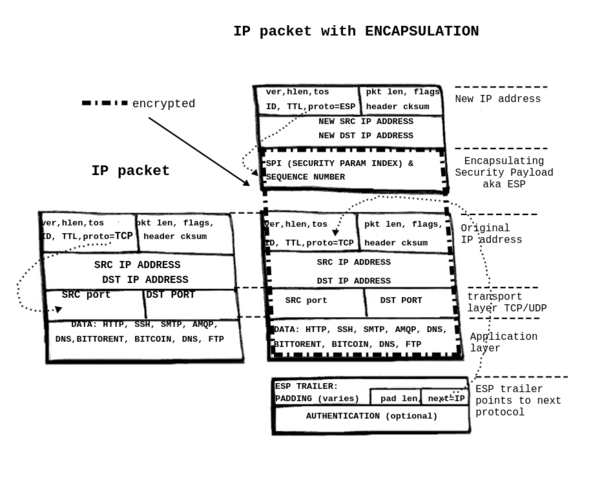
Looking at the initial architecture of the internet as a communication medium where any node could reach any other node – and where a node was authenticated by its address as a unique identifier – the current landscape has transformed into something quite different. Since the late 1990s, the IPv6 protocol was conceived to mitigate the depletion of IPv4 addresses[12] by providing a much larger address space, thereby restoring the original numeric uniqueness. IPv6 was also designed with embedded security within the IP packet itself. By contrast, IPv4 required external encryption configurations which led to the development of the IPSec encryption protocol in the mid-1990s. IPSec provided end-to-end security wrapped around the IP layer, authenticating and encrypting each IP packet. While IPSec ensured encryption for IPv4, it required additional software installation and configuration, but encryption was incorporated as a core component of IPv6.[13] For the vast majority of IPv4 based Internet communications that happen over the web, the solution to security was the implementation of HTTPS certificates,[14]. However, other internet connections – such as files syncing between two devices – require extra encryption configurations or tunnels, such ssh or VPN, or the IPSec mentioned above.
Secure certificates encrypt traffic over cables and wireless signals, but once data reach the destination server, they are no longer encrypted. Unencrypted data can therefore be cached and served by intermediaries located closer to users' internet access points. For example, when the same website is requested again, the content may be served by a Content Distribution Network (CDN) rather than the origin server. CDN providers deliver much of internet content by caching it on servers distributed around the world. By serving data from servers that are geographically close to users, they greatly reduce the impact of physical distance between the user’s internet access point and the origin server, thereby speeding up load times. However, this centralisation of content – which has been made possible by the sharp decline in digital storage costs since the 2010s – raises certain user‑rights concerns despite its performance benefits. Because CDNs terminate secure certificates and gain access to unencrypted data, they introduce an additional point where user data can be inspected, monitored or breached. Their central position also enables large‑scale blocking, filtering, and surveillance capitalism, which can affect, for example, the right to erasure – especially when data crosses borders.[15]
Technologies such as dynamic IP addresses, mentioned above – and other address-sharing technics[16] and CDNs that multiplex many sites onto fewer IPv4s working around the scarcity of IP addresses[17] – has slowed the IPv6 rollout across devices. Given IPv6 potential for true end-to-end encryption for each device on the internet, one might ask whether embedded per-packet encryption constitutes a civil right to security and privacy that industry and state surveillance actors would prefer to avoid. At the same time, ISPs can charge higher prices for scarce IPv4 addresses, and in some cases legacy IP blocks of addresses are traded on the grey market, because they were allocated before regional internet registries existed and therefore remain unregulated.[18]
It is interesting to consider a VPN as a means of rendering our data unreadable to non-consensual monitoring. In the case of the ServPub ambulant server – as a resistance to rigid university network configurations, and beyond its wider accessibility and mobility – the content traveling through private networks is encrypted and authenticated by design within the VPN software. This makes it unreadable, untraceable, and resistant to censorship. What also becomes untraceable is the geolocation of servers within the private network.
During the translation of the Tunnel Up/Tunnel Down Zine into Chinese,[19] the artist and translator Biyi Wen, referenced the art research project "A Tour of Suspended Handshakes." In this project, artist Cheng Guo physically visited nodes of China’s Great Firewall. Using network diagnostic tools, the artist identified the geolocations mapped to IP addresses of critical gateways that filter data from outside China,[20] drawing on data published by other researchers. These gateways' filtering function is what constitutes them as firewalls. At times, the locations visited by the artist corresponded to scientific and academic centres that could plausibly house gateway infrastructure. At other times, they led to desolate sites with no apparent technological presence. While Guo acknowledges that some gateways may be hidden or disguised – for example, antennas camouflaged as lamp posts – the primary reason for these discrepancies lies in the redistribution and resale of IP addresses. These factors make it difficult to pinpoint exact geographical locations. Moreover, mapping activities have been illegal in mainland China since 2002, and precise coordinates remain hidden from the public.[21]
In the case of the Great Firewall, the combination of IP redistribution and encrypted coordinates obscures the true geolocations of its gateways, rendering the firewall a nebulous and elusive system. For the ambulant servers, their exact geolocation remains similarly obscure because they are concealed within the virtual private network – beyond the main public-facing nodes such as Jean. However, unlike the Great Firewall, the concealment of the ambulant servers is not enforced through top-down governmental control. The desire to make home-based infrastructures addressable through a trusted network-sharing of tunnels and reverse proxies on community-run servers[22] creates the potential to circumvent censorship, surveillance, and content centralisation by CDNs, states or other institutional and commercial firewalls. In this way the imposed scarcity of IPv4 becomes a solidarity action.
It is worth mentioning here, Alison Macrina's work on the Library Freedom Project and Tor Browser as a concrete, real‑world activist case that reinforces the "messy, grinding labor of doing feminism." Alison's Library Freedom Project exemplifies this by turning libraries into practical privacy infrastructure sites: teaching surveillance resistance through Tor relays, anonymising traffic, and reclaiming data sovereignty – much like Systerserver and other community-run servers' VPNs, resist centralised control.
Digital literacies
Being part of the internet, or the internets,[23] creating and maintaining our own networked infrastructures involves an understanding of the technicalities and politics of IP addresses, routers and gateways, and the economy of IP scarcity and institutional and corporate control. One way of addressing the politics and economies of network infrastructures – and how we relate to technology – is by "following the data." Data is not just an informational unit or a technicality – it is how we as trans*feminists relate to computers, both on a supra- or infra-individual level and as something that can be incredibly personal and intimate. We need to keep asking: "Where is the data?" We need to develop technical awareness and accountability in how we participate in – and how we are complicit with – the infrastructures in which our data is created, stored, sold, and analysed. In "following the data," we become more engaged and cultivate our sensibilities around data and networked infrastructure politics.[24]
By making digital infrastructures and technicalities visible through drawings, diagrams, manuals, metaphors, performances, and gatherings, Systerserver traverses technical knowledge with the aim of de-clouding data,[25] and redistributing networks of machines and humans/species. Systerserver therefore becomes a space to exchange knowledge, whose sysadmins maintain and care together in non-hierarchical and non-meritocratic ways – what the sysadmins refer to as "feminist pedagogies." These pedagogies cultivate socio-technical learning by accepting diverse life experiences, recognising that knowledge is socially constructed, questioning digital hegemonies, and welcoming situated experiences from the places where people physically meet for the trans-feminist gatherings such as Eclectic Tech Carnival (/ETC), the TransHackFeminist Convergence (THF), and others. These meetings – or rather offline and online entanglements – encourage Do-It-Together practices, give time and space to study and write documentation, and collectivise moments of choosing our dependencies while feeling trusted in a safe(r) space to learn about technologies. They challenge our bodies-machines relations.
How can we imagine a virtual private server, in a material world? An intervention by ooooo and others during the rehabilitation of an eco-industrial colony in the mountains near Barcelona, Calafou, where a room was transformed into a physical public interface for the practices around the feminist server: anarchaserver.org.[26] Open for visitors, it was used during sysadmin work sessions, gatherings, sonic improvisations, and radio broadcasts. The door, windows, ceilings, and multi-levels served as analogies for the functionalities of a server’s hardware-software counterparts (ports, encryption, repositories, and even a firewall). It also included a bed, where someone could sleep, rest, and reside – in analogy with the Living Data container, which hosts ALEXANDRIA for wiki documentation and ZOIA HORN for multi-site blogging. The space was also activated during the THF Convergence, an event for intersectional feminists, queer, and trans people of all genders to better understand, use, and ultimately develop free and liberating technologies for social dissent.
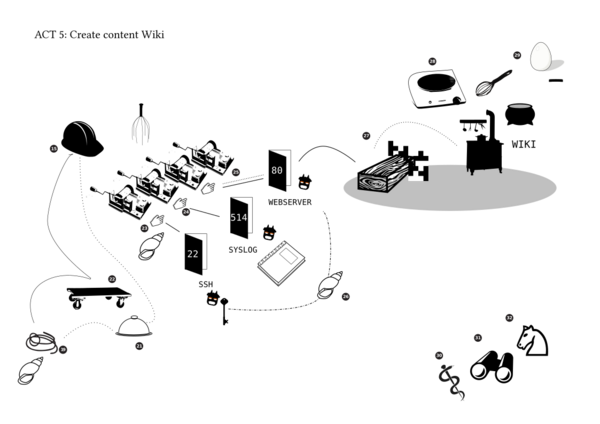
With the question "How to collectively embody a server?" ooooo staged another performative event during The Feminist Server Summit (12–15 December 2013),[27] organised by Constant association of media arts in Brussels. In Home is a Server, fourteen people were invited to choose a prop representing the different hardware parts of a computer (CPU, RAM, watchdogs, ports, kernels, hard drives). By reading a script together, they followed the data flow while installing a server, setting up a wiki, and publishing a recipe for pancakes – which they then made and ate together.
Are we vulnerable, safe, and do we need to encrypt? In different exercises combining dance notations, crypto techniques and careful somatic tactics, participants embody issues of security, privacy, safety and surveillance. Cryptodance was a performative event developed in August 2016 during the preparations for THF 2016!, by a small international constellation of choreographers, hackers, and dancers. [28]
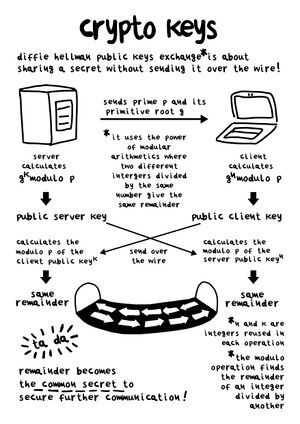
Crypto Keys is a drawing about the mathematical formulas used in the Diffie–Hellman algorithm for encrypting data over the internet without the need to exchange a password or secret key.
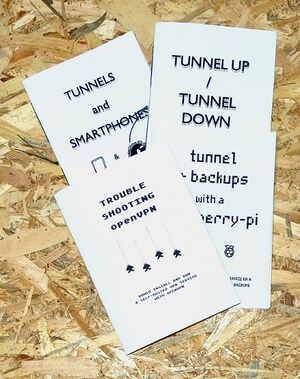
VPN introduction zines is a series of manuals about private virtual networks describing technical concepts of firewalls, authentication and encryption over the Internet, how we can install a VPN with a single board computer, on mobile phones, and when to chose for a VPN over a proxy.
What is feminist federation? Another example of making analogies and tangible translations, it the performative event Humming Birds. Through choreographies, sociometric exercises, and voicing techniques, participants explore the social network Fediverse and get introduced in a technical understanding of its protocol ActivityPub – a standard for publishing content in decentralised social networking.[29]
A feminist networking
"Technologies are about relations with things we would like to relate to, but also things we don't want to be related to." – Femke Snelting in Forms of Ongoingness (2018).[30]
A feminist server goes beyond a technically facilitated node in the network – it becomes an (online) space for understanding digital infrastructures and resisting hegemonies. It can be entered "as an inhabitant, to which we make contributions, nurture a safe space and a place for expression and experimentation, a place for taking a role in hacking heteronormativity and patriarchy."[31] A feminist server is a place where we as trans*feminists can share with intersectional, queer, and feminist communities – a place where our data and the contents of our websites are hosted, where we chat, store stories and imaginaries, and access the tools we need to get organised (mailing lists, calendars, Etherpads).
Serving, and becoming a server is not just a neutral relation between two or more computers.[32] It is tied to the politics of protocols, infrastructure capacity and power, responsibilities, dependencies, invisible labour, knowledge, and control. A feminist server is a space where we learn how a collective emancipation is possible from techno-fascist platforms and content service providers. As feminist servers, we refuse to be served in networks that increase our dependencies on cis male-dominated and extractivist technologies of big tech. Having a place – or "a room of one's own" – on the internet is therefore important, referencing historic feminist struggles for agency, and safe/r off- and online spaces for uninterrupted time together to imagine technological praxis in new ways.
Furthermore, the metaphor of one's own room[33] highlights the ways in which bodies need to be accommodated in the practices of feminist servers and social networking. These bodies incorporate our data bodies[34] but also the ways in which we show up in gatherings and places outside digital networks. Self-organised gatherings such as the Eclectic Tech Carnival (/ETC)[35] or the TransHackFeminist convergence (THF),[36] and feminist hacklabs such as marialab, fluid.space, mz balathazar’s laboratory, t_cyberhol, as well as (art) residencies or other larger gatherings (Global Gathering, Privacycamp, OFFDEM, Chaos Communication Congress) have been crucial in nurturing and fueling the desires for our own servers. These gatherings address the need to share ways of doing, tools and strategies to overcome and overthrow the monocultural, centralised, oligopolistic technologies of surveillance and control, and to resist the matrix of domination. These are moments where social networking can materialise into feminist servers and affective infrastructures.[37]
Social networking – which shapes affective infrastructures – can in this sense be laborious: an act of care, of wielding solidarities, of sharing and growing alliances, recognising our precarities, identities and collective oppressions. It is a community practice, a way of staying connected and connecting anew, of seeking and cherishing those critical connections that are always already more than technical.[38] Those critical connections can become feminist networking – a situated techno-political practice that engages us in more-than-human relations with hardware, wetware and software.
In terms of feminist servers, the server thus becomes a "connected room" or even '"infrastructures of one's own", characterised by the tension between the need for self-determination and the promiscuous, contagious practices of networking and making contact with others. These practices inherently surpass strong notions of the individual "self," facilitating instead a collective and heterogeneous search for empowerment, and contributing to improving conditions for networked subjectivities and solidarities. They transform into a connected room,[39] a network of one's own, with allies as co-dependencies – attributing value to each other(s), interacting as radical references[40] to evade hierarchies of cultural capital, and instead sustaining collective efforts of resistance against capitalistic logics of knowledge production.
When talking about the internet and its potential for feminist networking, one needs to move away from thinking of it as something "given" that we might "use". One must shift away from the cloudy image of cyberspace as an extension and intensification of capital, governance, and data power.[41]
ServPub, as a publishing platform for collaboration, learning digital infrastructuring while doing it, and being part of Systerserver's internet and networking, is moving toward feminist forms of affective infrastructures.
- ↑ Cait McKinney, Information Activism: A Queer History of Lesbian Media Technologies, (Duke University Press, 2020).
- ↑ For more information on the genealogy of Systerserver see Wessalowski, Nate & Karagianni, Mara. “From Feminist Servers to Feminist Federation.” A Peer-Reviewed Journal About 12, no. 1 (September 7, 2023), 192–208. https://doi.org/10.7146/aprja.v12i1.140450.
- ↑ Chapter 2: Traveling server space: Why does it matter?, "A Traversal Network of Feminist Servers" (2022). Accessed 8 March 2026. https://systerserver.net/ATNOFS/
- ↑ Systerserver hosts a GitLab instance as code repository, Peertube for video and streaming, Mailman for mailing lists, Nextcloud for data storage and collective organisation, Mastodon for providing a microblogging social networking platform, Tinc for VPN, and relevant code based projects and websites. For links to each service, visit https://systerserver.net/.
- ↑ Configuring a server requires what is known as a fixed IP address, which is a numeric notation, signalling the location of the server. This IP address can be mapped to a domain name, which in turn can be traceable on the internet when visiting said domain name in a browser.
- ↑ Rosa is Raspberry Pi server using varia.hub to be reachable on the internet. Varia hub is what in varia they call a jump hole, a poetic description for the VPN + reverse proxy through their servers. Varia is a space for developing collective approaches to everyday technology, working with free software, organising events, and collaborating in different constellations. See https://varia.zone/en/.
- ↑ XPUB is the Master of Arts in Fine Art and Design: Experimental Publishing of the Piet Zwart Institute in Rotterdam. XPUB focuses on the acts of making things public and creating publics in the age of post-digital networks. The VPN software Tinc and reverse proxy is inspired by their HUB project, which enabled the Institute to form an experimental server space for their students who could access the server from outside the Institute, passing institutional firewalls securely and let devices roam. See Docs:03_VPN_with_Tinc.
- ↑ Mara Karagianni, Michael Murtaugh, and Wendy Van Wynsberghe were commissioned by Constant to write a zine manual on Tinc and reverse proxies: "Making A Private server Ambulant", https://psaroskalazines.gr/pdf/rosa_beta_25_jan_23.pdf. The beta version of the zine was revised and updated by vo ezn, who is also part of Systerserver. She deployed it in the digital infrastructure of Hackers and Designers.
- ↑ IP address lease times provide security benefits such as preventing persistent unauthorised use, reduce risks such as IP spoofing and theft, and allow rapid response to misuse by removing compromised devices from the network.
- ↑ Networking! Ack! (2017), a zine by Julia Evans, provides a fun guide to DNS and computer networking in general. Accesssed 8 March 2026. https://jvns.ca/networking-zine.pdf.
- ↑ The internes stands for Systerserver's machines located in [mur.at] to reach a machine in Antwerp, which makes periodic backups of Jean and Adele servers. The network alliances stands for facilitating several home-based server initiatives within Systerserver's extensive community, such as the Etherpad services hosted on the leverburns server which Systerserver uses for technical documentation during server maintenance sessions, or for other allied communities such as caladona and brknhs that want to serve video content without having to commit to the expenses of acquiring a public and static IP address.
- ↑ The first publication of the IPv6 protocol in a Request for Comments was in December 1998. Accessed 20 September 2025. https://www.rfc-editor.org/rfc/rfc2460.txt.
- ↑ Besides being a secure protocol with extra authentication and privacy, IPv6 features support for unicast, multicast, and anycast. See, "Internet working with TCP/IP", Vol. 2 by Douglas E. Comer and David L. Stevens, (Prentice Hall, 1998). Accessed 20 September 2025. https://archive.org/details/internetworking000come.
- ↑ While HTTPS is a way to secure traffic over the internet, it is distinguished from IPSec in that IPSec secures all data traffic within an IP network, suitable for site-to-site connectivity. HTTPS –a secure version of HTTP, using TLS certificates –secures individual web sessions. The authentication with a TLS certificate relies on the organisation or company's name ownership of the certificate, and not on the integrity of the server's IP address. This enables CDNs to cache content and serve in place of the origin server, which contributes to the centralisation of content distribution over the web, https://gcore.com/learning/tls-on-cdn. For more about how TLS works, see https://www.bacloud.com/en/blog/190/ssl-for-ip-lets-encrypt-now-supports-tlsorssl-certificates-for-ip-addresses.html.
- ↑ For example, data harvesting and extensive users profiling without consent violates the EU law General Data Protection Regulation (GDPR), https://wideangle.co/blog/content-delivery-network-cdn-and-gdpr.
- ↑ For example, see routing via Network Address Translation (NAT), https://en.wikipedia.org/wiki/Network_address_translation.
- ↑ Huston Geoff, The IPv6 transition (2024). Accessed 20 September 2025. https://blog.apnic.net/2024/10/22/the-ipv6-transition/.
- ↑ The African continent registry (AFRINIC) has been under scrutiny due to organisational and legal problems. In 2019, 4.1 million IPv4 addresses (part of unused legacy IP blocks), were sold on the grey market. Accessed 25 July 2025. https://en.wikipedia.org/wiki/AFRINIC.
- ↑ Tunnel Up/Tunnel Down (2019), Mara Karagianni's self-published zine about what is a VPN and its various uses and technologies. Accessed 8 March 2026. https://psaroskalazines.gr/pdf/fanzine-VPN-screen-en.pdf.
- ↑ A gateway is a network device that acts as an entry and exit point between two different networks, translating and routing traffic so they can communicate. While a home or office router mainly forwards packets between networks that typically use IP, a gateway connects different kinds of networks and can translate between differnet protocols or data formats, and often operates across multiple OSI layers.
- ↑ See, https://en.wikipedia.org/wiki/Restrictions_on_geographic_data_in_China.
- ↑ Dynamic DNS (DDNS) is another option for when your ISP changes your home network's IP address.It is a commercial service that allows you also to use a fixed address for your home network. You can often set up DDNS on your router. Self-hosted websites or online resources will be redirected over commercial nodes maintained by companies – companies which are often known for data-exploitation, acts of censorship, and compliance with states agencies in cases of political prosecution.
- ↑ Networks with an Attitude was a work session exploring the future of Internet, organised by Constant from 7 to 13 April 2019 at various locations in Antwerp. The internet is dead, long live the internets! Accessed on 8 March 2026. https://constantvzw.org/sponge/s/?u=https://www.constantvzw.org/site/-Networks-with-an-Attitude-.html.
- ↑ Gray Jonathan, Gerlitz Carolin, Bounegru Liliana, “Data Infrastructure Literacy.” Big Data & Society 5, no. 2 (1 July 2018). https://doi.org/10.1177/2053951718786316
- ↑ Hilfling Ritasdatter Linda, Gansing Kristoffer, "A Video Store After the End of the World". Accessed 8 March 2026. https://vhs.data.coop/.
- ↑ The documentation of this process https://zoiahorn.anarchaserver.org/physical-process/ is hosted on the AnarchaServer: an allied feminist server – set up in Calafou, Spain – that contributes to the maintenance of autonomous infrastructure on the internet for feminists projects.
- ↑ The 14th edition of the Verbindingen/Jonctions gathering organised by constant vzw in December 2013 was dedicated to a feminist review of mesh, cloud, autonomous, and DIY servers. Accessed 8 March 2026. https://areyoubeingserved.constantvzw.org/Summit.xhtml.
- ↑ Goldjian and bolwerK started plotting the Cryptodance project during a Ministry of Hacking (hosted by esc in Graz, Austria), where they formed a joint (ad)venture of the Department of Waves and Shadow and the Department of Care and Wonder. Cryptodance was also shown in THF 2016 (Montréal) and Panke Gallery (Berlin).
- ↑ Nate Wessalowski and xm developed it during 360 degrees of proximities for the cyborg collective of Caladona, a women center in Barcelona, together with whom they installed peertube on a self-hosted server. ActivityPub provides a client-to-server API for creating and modifying content, as well as a federated server-to-server protocol for delivering notifications and content to other servers.
- ↑ Sollfrank, Cornelia, "Forms of Ongoingness". Interview with Femke Snelting and spideralex. House for Electronic Arts (HeK). (18 September 2018). Accessed on 8 March 2026. https://creatingcommons.zhdk.ch/wp-content/uploads/2020/06/Transcript-Femkespider.pdf.
- ↑ Spideralex in Sollfrank, Cornelia, "Forms of Ongoingness". House for Electronic Arts (HeK) (18 September 2018). Accessed on 8 March 2026. https://creatingcommons.zhdk.ch/wp-content/uploads/2020/06/Transcript-Femkespider.pdf.
- ↑ Gargaglione, Erika, “Hacking Maintenance With Care Reflections on the Self-administered Survival of Digital Solidarity Networks", Roots§Routes (14 May 2023). Accessed 8 March 2026. https://www.roots-routes.org/hacking-maintenance-with-care-reflections-on-the-self-administered-survival-of-digital-solidarity-networks-by-erica-gargaglione/. [client/server not user/developer].
- ↑ "Networks of One’s Own" is a periodic para-nodal publication by varia (September 2019). Accessed 8 March 2026. https://networksofonesown.varia.zone/.
- ↑ Association for Progressive Communications, Paz Peña and Joana Varon, “Consent to Our Data Bodies: Lessons From Feminist Theories to Enforce Data Protection”, Coding Rights (25 March 2019), https://www.apc.org/en/pubs/consent-our-data-bodies-lessons-feminist-theories-enforce-data-protection.
- ↑ The Eclectic Tech Carnival (/ETC) is a potent gathering of feminists who critically explore and develop everyday skills and information technologies in the context of free software and open hardware. /ETC chews on the roots of control and domination, disrupts patriarchal societies, and imagines better alternatives, https://monoskop.org/Eclectic_Tech_Carnival.
- ↑ See, https://alexandria.anarchaserver.org/index.php/Main_Page#TransHackFeminist_Convergence.
- ↑ Nate Wessalowski & Mara Karagianni, “From Feminist Servers to Feminist Federation.” A Peer-Reviewed Journal About 12, no. 1 (7 September 2023), 192–208, https://doi.org/10.7146/aprja.v12i1.140450.
- ↑ Following a quote from Grace Lee Hoggs on connectedness and activism which puts "critical connections" over "critical mass" after an idea by Margaret Wheatly, Boggs, G., Kurashige, S. The Next American Revolution: Sustainable Activism for the Twenty-First Century. (University of California Press, 2012), 50.
- ↑ See also spideralex, referencing Remedios Zafra's book, A Connected Room of One’s Own, https://www.remedioszafra.net/aconnectedroom.html in Cornelia Sollfrank, "Forms of Ongoingness. Interview with Femke Snelting and spideralex." House for Electronic Arts (HeK), Basel. (18 September, 2018) https://creatingcommons.zhdk.ch/wp-content/uploads/2020/06/Transcript-Femkespider.pdf
- ↑ A term introduced in this book by ooooo, which then got picked up an led to an in depth article on the subject in Chapter_5b:_Distribution.
- ↑ Metahaven, Daniel van der Velden, Vinca Kruk, "Captives of the Cloud: Part I,", e-flux 37 (2012). https://www.e-flux.com/journal/37/61232/captives-of-the-cloud-part-i.